【影视趣谈】对于“间谍”的中性解释,这个比较靠谱
【Movie Farce】The Nutural Explaination of "Spy"
一说到间谍,人的心理状态常常会变得比较High,招蜂引谍(蝶),这是事实,神经心理学家们对此很有研究。而对于“间谍”的中性解释,下面的这个解释就比较靠谱。
说起与“间谍”有关的电影,就艺术性和观赏性而言,稚雨还是比较欣赏《沉默的人》(点击在线看)、《北非谍影》(点击在线看)和《海军上尉巴宁》,。。。,呵呵。
《沉默的人》,不说别的,只要看一下它的配音班子的阵容,就知道那是何等的出色。高博先生,上影演员,客串为上海电影译制厂,为影片主角克莱芒·蒂贝尔(哈里科夫)配音。他以前就住在上海徐汇区的延庆路4弄里。夏日炎炎,卖西瓜的农民兄弟,踏着满载西瓜的黄鱼车到处兜弄堂叫卖。这时候,高博先生,穿着圆领老头衫,手持芭蕉扇,往往会来挑西瓜。高博先生,笑呵呵的,没啥架子,待农民兄弟特和气,要是不挑明的话,谁也不知道他是上影厂大名鼎鼎的演员。那时的稚雨,小不点儿大,帮着妈妈一起买西瓜,就爱凑着往黄鱼车边上靠,不为别的,为的就是要听听高爷爷那磁石般的嗓音啊。。。
《北非谍影》,。。。
《海军上尉巴宁》,。。。
When it comes to "Spy" discussion, a person's psychological state often becomes "Getting high"(slang), "Attracting bees and flirting butterflies"(Chinese proverb), this is true, neuropsychologists have been researching this subject quite well. As for a neutral explanation of "spy", the following Wiki explanation is more reliable.
Speaking about the "spy" movies, on the artistic and ornamental senses, these are my favourite: "Le Silencieux", "Casablanca" and "Navy Captain Baning", ... ho-ho.
"Le Silencieux"(click to watch online), ...
"Casablanca"(click to watch online), ...
"Navy Captain Baning", ...
~~~~~~~~~~~~~~~~~~~~~~~~~~~
间谍
| 此条目需要补充更多来源。(2009年11月20日) 请协助添加来自可靠来源的引用以改善这篇条目。无法查证的内容会被提出异议而移除。 |
| 战争 |
| 军事史 |
|
显示▼时代
|
|
显示▼战争方式
|
|
显示▼战场
|
|
显示▼武器
|
|
显示▼战术
|
|
显示▼战略
|
|
显示▼军事组织
|
|
显示▼后勤
|
|
显示▼法律
|
|
显示▼政治
|
|
显示▼军事研究
|
|
显示▼列表
|
间谍是指从事秘密侦探工作的人,古代亦称作细作,深入敌方内部的称为卧底。从敌对方或竞争对手那里刺探机密情报或是进行破坏活动,以此来使其所效力的一方有利。根据工作目的地不同,间谍大致分为军事间谍和工业间谍(或称商业间谍、经济间谍)。有时间谍为敌对多方同时服务,称为“多重间谍”或“多面谍”。
目录[隐藏] |
[编辑] 内容
间谍活动是为某政府效力的一部分。换言之,政府是支持间谍活动的。“间谍”一词很容易被人联想成:某一个主权国家监视著自己的敌国。最早开始,间谍是用来刺探军事方面的,但现今则蔓延至公司方面(俗称工业间谍)。现时,有不少国家都会惯常地派出间谍去监视自己的敌人和盟友,但他们从不将这些资料透露给大众。另外,经常运用间谍的国家,往往都会去组织一个特别的公司来表代他们,例如:国际私人军事保安组织(SCG International Risk)。1990年的布莱克法律词典(Black's Law Dictionary)将动词“间谍”下了一个定议,意为:“……收集、传送或泄漏关于国防的情报”。
名词“情报人员”,即间谍,也就是专门被雇来做这种事的人。他代表军队、警察或情报机构里面其中一员。他们专门去收集、融合和分析取回来的情报,以方便给政府提供对策。大体来说,情报人员往往会潜入对方的国家,然后收集和运行情报。这就成为了他们自己国家的间谍。我们称这类间谍为“鼹鼠”(mole)或“投诚者”(defector)。
[编辑] 历史
很多关于间谍的事件都被保存至历史内。而古代的著作例如:中国的《孙子兵法》,和著名的印度军事专家考底利耶。《孙子兵法》还将间谍分成乡间(又称因间,敌人的同乡)、内间(敌国的官吏)、反间(收买敌人的间谍)、死间(向敌人散布谣言,事败后,间谍必死)、生间(能活着回来的间谍)五种。秦国末年刘邦在攻取齐国时,派出辩士郦食其前往游说,劝齐王投降,韩信在齐王投降之际却加紧攻齐。最后郦食其遭煮杀,这是死间。国共内战后期,胡宗南发现熊向晖是共产党派来的间谍,却不敢向上层报告,只好把他送出国念书[1],这是生间的代表作。
考底利耶的学徒,旃陀罗笈多 ,即印度孔雀王朝的开国君主,熟用了暗杀和间谍活动等技巧,并将这些技巧写在《政事论》(Arthashastra)里。此外,希伯来人和古埃及人也有研究和使用到间谍的策略。在日本封建历史上,君主们亦会使用忍者来收集敌军的情报。到了近代,例如在英格兰女王伊丽莎白的统治下,间谍更是扮演着一个很重要的角色。至于现代的间谍手法,当然会比以前的更加精彩。
于冷战时期,苏联和美国(及其他可能的国家)也极度地使用间谍,以收集关于核武器的秘密情报。但在现时,间谍手法则是用来对付那些,被视为是“恐怖份子”的毒品走私交易。在这三十年里,美国不断地提高自己国家的间谍技巧,来盗取与控制敌方的情报。随着现代的技术迅速发展,举个例子,像尼克森总统使用窃听器一事(俗称水门事件),和里根总统运用梯队系统和Carnivore手法来防范敌人的间谍入侵,包括监视所有电子通讯仪器(例如手机、语音讯箱和电邮等等)。
二十世纪六十年代,海峡两岸亦曾进行过为数不少的谍战,而两岸之间直到2011年仍然有互派间谍,如2011年台湾方面的罗贤哲少将便被揭发为大陆间谍,其潜伏达八年之久,也是迄今为止,台湾所查出最高职位的间谍,引起台湾朝野震撼。
另外,苏联声称自己拥有最先进的网络间谍,并能潜入敌人的保安地区,也因而引起了许多丑闻。
[编辑] 风险
间谍活动的风险总是在变化,举一个例子,譬如一名间谍在其他的国家内,违反了当地的法规,就会被人以间谍罪名放逐、囚禁,或甚至被处死。如果在自己的国家里犯了法,则会被以叛国的罪名囚禁,同样有机会被处死(罗森堡即属一例)。另外,有一位美国中央情报局官员,名叫Aldrich Ames,他因将情报偷卖给苏联的国家安全委员会,而被联邦调查局拘捕,更会有可能面对终身监禁。虽然拥有外交豁免权, 但他仍被人视为“不受欢迎的人”(拉丁文:persona non grata),然后被带往机场。Ames的妻子害怕如果丈夫不遵守这些条件的话,可能会被判终身监禁。所以,Ames选择遵守,而最终则被监禁五年。弗朗 西斯·莱德蒙德(Hugh Francis Redmond),同样也是一位美国中央情报局官员,因为窥探中国的情报而被监禁了19年,更死在那里。
于英国居住的前苏联克格勃上校利特维年科(俄文:Александр Вальтерович Литвиненко),遭遇历史上最昂贵的投毒[2]——价值三千万欧元的钋-210,创造了另类的吉尼斯世界纪录。[3]
一些从事间谍活动的警察亦被称作“卧底”或“边缘人”,其人身及心理方面的风险程度亦很高。因为此项任务通常由年轻的警员担当数月,数年甚至更长时间搜集犯罪集团的证据,而任务成功的前提往往是必须取得对方的信任方可实现,当事人亦会牺牲自己的亲情,爱情,友情,甚至一些警方卧底因为需要博取对方信任,拥有极大地大无畏精神,以身试法进行贩毒,吸毒,军火买卖或伤害他人身体的非法活动,对于他们的自身健康和心理状态产生严重的后果和负担,当任务一经成功,这种牺牲自我保全大多数警队同僚的方式往往会得到警队内部乃至政府方面的丰厚嘉奖,但只要失败一次,其生命亦会受到非常严重的威胁。
在近代的一些电影或电视中,警队与黑帮的卧底题材取得了一定程度的成功,因为剧情往往比较刺激,受到影迷的热捧,比较著名的有中国电视剧《潜伏》、《敌营十八年》,英国电影《007》系列,美国电影荷里活《职业特工队》系列,香港电影《门徒》和《无间道》系列等等。
[编辑] 技术
技术情报方面的经费往往超过了人员费用,美国在这方面的比例是七比一。
[编辑] 注释
- ^ 何炳棣:《读史阅世六十年》
- ^ 专家解析俄叛逃特工离奇死亡之谜
- ^ 俄叛逃特工体内钋价近三千万欧元 可毒死百余人--国际--人民网
[编辑] 参看
Espionage
Espionage or spying involves a government or individual obtaining information that is considered secret or confidential without the permission of the holder of the information. Espionage is inherently clandestine, as it is taken for granted that it is unwelcome and punishable by the prospective victim. Is it a subset of intelligence gathering - which otherwise may be conducted from public sources and using perfectly legal and ethical means.
Espionage is usually part of an institutional effort by a government or corporation, and the term is most readily associated with state spying on potential or actual enemies primarily for military purposes. Spying involving corporations is known as industrial espionage.
One of the most effective ways to gather data and information about an enemy (or potential enemy) is by infiltrating the enemy's ranks. This is the job of the spy (espionage agent). Spies can bring back all sorts of information concerning the size and strength of an enemy army. They can also find dissidents within the enemy's forces and influence them to defect. In times of crisis, spies can also be used to steal technology and to sabotage the enemy in various ways. Counterintelligence operatives can feed false information to enemy spies, protecting important domestic secrets and preventing attempts at subversion. Nearly every society has very strict laws concerning espionage, and the penalty for being caught is often severe. However, the benefits that can be gained through espionage are generally felt to outweigh the risks.
Further information on clandestine HUMINT (human intelligence) information collection techniques is available, including discussions of operational techniques, asset recruiting and the tradecraft used to collect this information.
[edit] History
Events involving espionage are well documented throughout history. The ancient writings of Chinese and Indian military strategists such as Sun-Tzu and Chanakya contain information on deception and subversion. Chanakya's student Chandragupta Maurya, founder of the Maurya Empire in India, made use of assassinations, spies and secret agents, which are described in Chanakya's Arthasastra. The ancient Egyptians had a thoroughly developed system for the acquisition of intelligence, and the Hebrews used spies as well, as in the story of Rahab. Spies were also prevalent in the Greek and Roman empires.[1] During the 13th and 14th centuries, the Mongols relied heavily on espionage in their conquests in Asia and Europe. Feudal Japan often used ninja to gather intelligence. More recently, spies played a significant part in Elizabethan England (see Francis Walsingham). Many modern espionage methods were well established even then.[2] Aztecs used Pochtecas, people in charge of commerce, as spies and diplomats, and had diplomatic immunity.
The Cold War involved intense espionage activity between the United States of America and its allies and the Soviet Union and the People's Republic of China and their allies, particularly related to nuclear weapons secrets. Recently, espionage agencies have targeted the illegal drug trade and those considered to be terrorists. Since 2008 the United States has charged at least 57 defendants for attempting to spy for China.[3]
Different intelligence services value certain intelligence collection techniques over others. The former Soviet Union, for example, preferred human sources over research in open sources, while the United States has tended to emphasize technological methods such as SIGINT and IMINT. Both Soviet political (KGB) and military intelligence (GRU[4]) officers were judged by the number of agents they recruited.
[edit] Targets of espionage
Espionage agents are usually trained experts in a specific targeted field. This allows them to differentiate mundane information from a target which has intrinsic value to own organisational development. Correct identification of the target at its execution is the sole purpose of the espionage operation.
The broad areas of espionage targeting expertise are:
- Natural resource strategic production identification and assessment (food, energy, materials)
- Agents are usually found among bureaucrats that administer these resources in own countries
- Popular sentiment towards domestic and foreign policies (popular, middle class, elites)
- Agents often recruited from field journalistic crews, exchange postgraduate students and sociology researchers
- Strategic economic strengths (production, research, manufacture, infrastructure)
- Agents recruited from science and technology academia, commercial enterprises, and more rarely from military technologists
- Military capability intelligence (offensive, defensive, manoeuvre, naval, air, space)
- Agents are trained by special military espionage education facilities, and posted to area of operation with covert identities to prevent prosecution
- Operations specifically targeting opponents' intelligence services themselves, such as breaching confidentiality of communications, recruiting defectors or moles
[edit] Methods and terminology
While news media may speak of "spy satellites" and the like, espionage is not a synonym for all intelligence functions. It is a specific form of human source intelligence (HUMINT). Codebreaking (cryptanalysis or COMINT), aircraft or satellite photography (IMINT) and research in open publications (OSINT) are all intelligence gathering disciplines, but none of them are espionage. Many HUMINT activities, such as prisoner interrogation, reports from military reconnaissance patrols and from diplomats, etc., are not espionage.
Unlike other forms of intelligence collection disciplines, espionage usually involves accessing the place where the desired information is stored, or accessing the people who know the information and will divulge it through some kind of subterfuge. There are exceptions to physical meetings, such as the Oslo Report, or the insistence of Robert Hanssen in never meeting the people to whom he was selling information.
The US defines espionage towards itself as "The act of obtaining, delivering, transmitting, communicating, or receiving information about the national defense with an intent, or reason to believe, that the information may be used to the injury of the United States or to the advantage of any foreign nation. Black's Law Dictionary (1990) defines espionage as: "...gathering, transmitting, or losing...information related to the national defense". Espionage is a violation of United States law, 18 U.S.C. §§ 792–798 and Article 106 of the Uniform Code of Military Justice".[5] The United States, like most nations, conducts espionage against other nations, under the control of the National Clandestine Service. Britain's espionage activities are controlled by the Secret Intelligence Service.
[edit] Organization
A spy is a person employed to obtain such secrets. Within the United States Intelligence Community, "asset" is a more common usage. A case officer, who may have diplomatic status (i.e. official cover or non-official cover), supports and directs the human collector. Cutouts are couriers who do not know the agent or case officer, but transfer messages. A safe house is a refuge for spies.
In larger networks the organization can be complex with many methods to avoid detection, including clandestine cell systems. Often the players have never met. Case officers are stationed in foreign countries to recruit and to supervise intelligence agents, who in turn spy on targets in their countries where they are assigned. A spy need not be a citizen of the target country - hence does not automatically commit treason when operating within it. While the more common practice is to recruit a person already trusted with access to sensitive information, sometimes a person with a well-prepared synthetic identity, called a Legend in tradecraft, may attempt to infiltrate a target organization.
These agents can be moles (who are recruited before they get access to secrets), defectors (who are recruited after they get access to secrets and leave their country) or defectors in place (who get access but do not leave).
Spies may also be used to spread disinformation in the organization in which they are planted, such as giving false reports about their country's military movements, or about a competing company's ability to bring a product to market. Spies may be given other roles that also require infiltration, such as sabotage.
Many governments routinely spy on their allies as well as their enemies, although they typically maintain a policy of not commenting on this. Governments also employ private companies to collect information on their behalf such as SCG International Risk and others.
[edit] Industrial espionage
Reportedly Canada is losing $12 billion[6] and German companies are estimated to be losing about €50 billion ($87 billion) and 30,000 jobs[7] to industrial espionage every year.
[edit] Agents in espionage
In espionage jargon, an agent refers to the person who does the spying; a citizen of one country who is recruited by a second country to spy on or work against his own country. In popular usage, this term is often erroneously applied to a member of an intelligence service who recruits and handles agents; in espionage such a person is referred to as an intelligence officer or case officer. There are several types of agent in use today.
- Double agent, "is a person who engages in clandestine activity for two intelligence or security services (or more in joint operations), who provides information about one or about each to the other, and who wittingly withholds significant information from one on the instructions of the other or is unwittingly manipulated by one so that significant facts are withheld from the adversary. Peddlers, fabricators, and others who work for themselves rather than a service are not double agents because they are not agents. The fact that doubles have an agent relationship with both sides distinguishes them from penetrations, who normally are placed with the target service in a staff or officer capacity."[8]
- Re-doubled agent, an agent who gets caught as a double agent and is forced to mislead the foreign intelligence service.
- Unwitting double agent, an agent who offers or is forced to recruit as a double or re-doubled agent and in the process is recruited by either a third party intelligence service or his own government without the knowledge of the intended target intelligence service or the agent. This can be useful in capturing important information from an agent that is attempting to seek allegiance with another country. The double agent usually has knowledge of both intelligence services and can identify operational techniques of both, thus making third party recruitment difficult or impossible. The knowledge of operational techniques can also effect the relationship between the Operations Officer (or case officer) and the agent if the case is transferred by an Operational Targeting Officer to a new Operations Officer, leaving the new officer vulnerable to attack. This type of transfer may occur when an officer has completed his term of service or when his cover is blown.
- Triple agent, an agent that is working for three intelligence services.
- Unwitting double agent, an agent who offers or is forced to recruit as a double or re-doubled agent and in the process is recruited by either a third party intelligence service or his own government without the knowledge of the intended target intelligence service or the agent. This can be useful in capturing important information from an agent that is attempting to seek allegiance with another country. The double agent usually has knowledge of both intelligence services and can identify operational techniques of both, thus making third party recruitment difficult or impossible. The knowledge of operational techniques can also effect the relationship between the Operations Officer (or case officer) and the agent if the case is transferred by an Operational Targeting Officer to a new Operations Officer, leaving the new officer vulnerable to attack. This type of transfer may occur when an officer has completed his term of service or when his cover is blown.
- Re-doubled agent, an agent who gets caught as a double agent and is forced to mislead the foreign intelligence service.
- Intelligence agent: Provides access to sensitive information through the use of special privileges. If used in corporate intelligence gathering, this may include gathering information of a corporate business venture or stock portfolio. In economic intelligence, "Economic Analysts may use their specialized skills to analyze and interpret economic trends and developments, assess and track foreign financial activities, and develop new econometric and modeling methodologies."[9] This may also include information of trade or tariff.
- Access agent: Provides access to other potential agents by providing profiling information that can help lead to recruitment into an intelligence service.
- Agent of influence: Someone who may provide political influence in an area of interest or may even provide publications needed to further an intelligence service agenda. I.e. The use of the media to print a story to mislead a foreign service into action, exposing their operations while under surveillance.
- Agent provocateur: This type of agent will instigate trouble or may provide information to gather as many people as possible into one location for an arrest.
- Facilities agent: A facilities agent may provide access to buildings such as garages or offices used for staging operations, resupply, etc.
- Principal agent: This agent functions as a handler for an established network of agents usually Blue Chip.
- Confusion agent: May provide misleading information to an enemy intelligence service or attempt to discredit the operations of the target in an operation.
- Sleeper agent: A sleeper agent is a person who is recruited to an intelligence service to wake up and perform a specific set of tasks or functions while living under cover in an area of interest. This type of agent is not the same as a deep cover operative who is continually in contact with their case officer in order to file intelligence reports. A sleeper agent will not be in contact with anyone until activated.
- Illegal agent: This is a person who is living in another country under false credentials that does not report to a local station. A non official cover operative is a type of cover used by an intelligence operative and can be dubbed an "Illegal"[10] when working in another country without diplomatic protection.
[edit] Law
Espionage is a crime under the legal code of many nations. The risks of espionage vary. A spy breaking the host country's laws may be deported, imprisoned, or even executed - especially in wartime, a summary execution may well be the penalty. A spy breaking his/her own country's laws can be imprisoned for espionage or/and treason, or even executed, as the Rosenbergs were. For example, when Aldrich Ames handed a stack of dossiers of CIA agents in the Eastern Bloc to his KGB-officer "handler", the KGB "rolled up" several networks, and at least ten people were secretly shot. When Ames was arrested by the FBI, he faced life in prison; his contact, who had diplomatic immunity, was declared persona non grata and taken to the airport. Ames's wife was threatened with life imprisonment if her hu*****and did not cooperate; he did, and she was given a five-year sentence. Hugh Francis Redmond, a CIA officer in China, spent nineteen years in a Chinese prison for espionage—and died there—as he was operating without diplomatic cover and immunity.[citation needed]
Many organizations, both national and non-national, conduct espionage operations. It should not be assumed that espionage is always directed at the most secret operations of a target country. National and terrorist organizations and other groups are also targets.[citation needed]
Communications both are necessary to espionage and clandestine operations, and also a great vulnerability when the adversary has sophisticated SIGINT detection and interception capability. Agents must also transfer money securely.[citation needed]
The United States in World War I passed the Espionage Act of 1917. Over the years many spies, such as the Soble spy ring, Robert Lee Johnson, the Rosenberg ring, Aldrich Hazen Ames,[11] Robert Philip Hanssen,[12] Jonathan Pollard, John Anthony Walker, James Hall III, and others have been prosecuted under this law.
However espionage laws are also used to prosecute non-spies. In the United States the Espionage Act of 1917 was used against socialist politician Eugene V. Debs. It was later used to suppress publication of periodicals, for example of Father Coughlin in WWII. In the early 21st century, the act was used to prosecute officials who communicated with US journalists, such as Thomas Andrews Drake and Stephen Jin-Woo Kim[13]
[edit] List of famous spies
|
|
This article is in a list format that may be better presented using prose. You can help by converting this article to prose, if appropriate. Editing help is available. (March 2010) |

[edit] Espionage under Elizabeth I of England
[edit] Espionage in the American Revolution
- Thomas Knowlton, The First American Spy
- Nathan Hale
- John Andre
- James Armistead
[edit] Espionage in the Napoleonic Wars
George Adams
[edit] Espionage in the American Civil War
One of the innovations in the American Civil War was the use of proprietary companies for intelligence collection. See Allan Pinkerton.
[edit] Espionage in the Aceh War
Dutch professor Snouck Hurgronje world leading authority on Islam was a proponent of espionage to quell Muslim resistance in Aceh in the Dutch East Indies. In his role as Colonial Advisor of Oriental affairs he gathered intelligence under the name "Haji Abdul Ghaffar".
His knowledge of Islamic and Aceh culture enabled him to devise strategies which significantly helped crush the resistance of the Aceh inhabitants and impose Dutch colonial rule on them, ending the 40 year Aceh War with varying casualty estimates of between 50,000 and 100,000 inhabitants dead and about a million wounded.
[edit] Espionage in the Second Boer War
[edit] Espionage in World War I
[edit] Espionage in World War II
Informants were common in World War II. In November 1939, the German Hans Ferdinand Mayer sent what is called the Oslo Report to inform the British of German technology and projects in an effort to undermine the Nazi regime. The Réseau AGIR was a French network developed after the fall of France that reported the start of construction of V-weapon installations in Occupied France to the British.
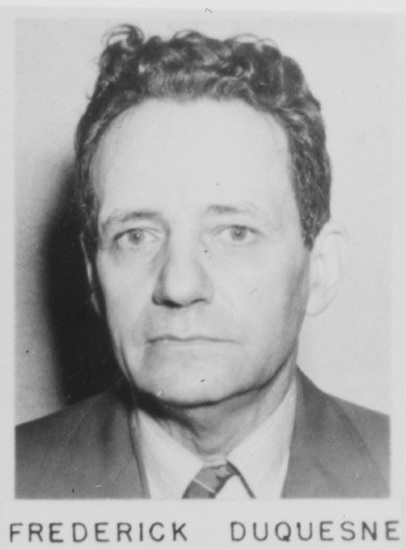
Counterespionage included the use of turned Double Cross agents to misinform Nazi Germany of impact points during the Blitz and internment of Japanese in the US against "Japan's wartime spy program". Additional WWII espionage examples include Soviet spying on the US Manhattan project, the German Duquesne Spy Ring convicted in the US, and the Soviet Red Orchestra spying on Nazi Germany. The US lacked a specific agency at the start of the war, but quickly formed the Office of Strategic Services (OSS).
Spying has sometimes been considered a gentlemanly pursuit, with recruiting focused on military officers, or at least on persons of the class from whom officers are recruited. However, the demand for male soldiers, an increase in women's rights, and the tactical advantages of female spies led the Special Operations Executive (SOE) to set aside any lingering Victorian Era prejudices and begin employing them in April 1942.[citation needed] Their task was to transmit information from Nazi occupied France back to Allied Forces. The main strategic reason was that men in France faced a high risk of being interrogated by Nazi troops but women were less likely to arouse suspicion. In this way they made good couriers and proved equal to, if not more effective than, their male counterparts. Their participation in Organization and Radio Operation was also vital to the success of many operations, including the main network between Paris and London.
- See also Honeypot
[edit] Espionage post World War II
In the United States, there are several federal agencies that form the United States Intelligence Community. The Central Intelligence Agency operates a Clandestine Service (NCS)[15] to collect human intelligence and perform Covert operations.[16] The National Security Agency collects Signals Intelligence. Other agencies do similar work. The CIA used to head the IC but after the September 11 attacks a new agency was formed, the Director of National Intelligence, to lead the group.
[edit] Espionage technology and techniques
[edit] Spy fiction
| This section does not cite any references or sources. Please help improve this section by adding citations to reliable sources. Unsourced material may be challenged and removed. (July 2011) |
An early example of espionage literature is Kim by the English novelist Rudyard Kipling, with a description of the training of an intelligence agent in the Great Game between the UK and Russia in 19th century Central Asia. An even earlier work was James Fenimore Cooper's classic novel, The Spy, written in 1821, about an American spy in New York during the Revolutionary War.
During the many 20th century spy scandals, much information became publicly known about national spy agencies and dozens of real-life secret agents. These sensational stories piqued public interest in a profession largely off-limits to human interest news reporting, a natural consequence of the secrecy inherent to their work. To fill in the blanks, the popular conception of the secret agent has been formed largely by 20th and 21st century literature and cinema. Attractive and sociable real-life agents such as Valerie Plame find little employment in serious fiction, however. The fictional secret agent is more often a loner, sometimes amoral—an existential hero operating outside the everyday constraints of society. Loner spy personalities may have been a stereotype of convenience for authors who already knew how to write loner private investigator characters that sold well from the 1920s to the present.
Johnny Fedora achieved popularity as a fictional agent of early Cold War espionage, but James Bond is the most commercially successful of the many spy characters created by intelligence insiders during that struggle. His less fantastic rivals include Le Carre's George Smiley and Harry Palmer as played by Michael Caine.
Jumping on the spy bandwagon, other writers also started writing about spy fiction featuring female spies as protagonists, such as The Baroness, which has more graphic action and sex, as compared to other novels featuring male protagonists.
[edit] See also
- Nations
- People
- Artifacts
- Types
[edit] References
|
|
This article includes a list of references, but its sources remain unclear because it has insufficient inline citations. Please help to improve this article by introducing more precise citations. (April 2009) |
- ^ "Espionage in Ancient Rome". HistoryNet.
- ^ Henrywotton.org.uk
- ^ Arrillaga, Pauline. "China's spying seeks secret US info." AP, 7 May 2011.
- ^ Suvorov, Victor (1987). Inside the Aquarium. Berkley. ISBN 042509474X.
- ^ US Department of Defense (2007-07-12). "Joint Publication 1-02 Department of Defense Dictionary of Military and Associated Terms" (PDF). Retrieved 2007-10-01.
- ^ "Defectors say China running 1,000 spies in Canada". CBC News. June 15, 2005.
- ^ "Beijing's spies cost German firms billions, says espionage expert". The Sydney Morning Herald. July 25, 2009.
- ^ "Double Agent". cia.gov.
- ^ Cia.gov
- ^ Illegal Mi5.gov -How spies operate.
- ^ "Aldrich Ames Criminal Complaint". jya.com. Retrieved 2011 03 19.
- ^ "USA v. Robert Philip Hanssen: Affidavit in Support of Criminal Complaint, Arrest Warrant and Search Warrant". fas.org. Retrieved 2011 03 19.
- ^ Josh Gerstein (11.3.7). "Despite openness pledge, President Obama pursues leakers". politico.com. Retrieved 2011 03 19.
- ^ Famous Spies in History, CNN
- ^ "Offices of CIA > Clandestine Service > Who We Are". cia.gov. Retrieved 2010-06-18.
- ^ "Offices of CIA > Clandestine Service > Our Mission". cia.gov. Retrieved 2010-06-18.
[edit] Further reading
- Jenkins, Peter Surveillance Tradecraft: The Professionals Guide to Surveillance Training ISBN 978-9535378-22
- Felix, Christopher A Short Course in the Secret War, 4th Edition Madison Books November 19, 2001
- West, Nigel MI6: British Secret Intelligence Service Operations 1909-1945 1983
- Smith Jr., W. Thomas Encyclopedia of the Central Intelligence Agency 2003
- Richelson, Jeffery T. The U.S. Intelligence Community 1999 fourth edition
- Richelson, Jeffery T. A Century of Spies: Intelligence in the Twentieth Century 1977
- Owen, David Hidden Secrets: A Complete History of Espionage and the Technology Used to Support It
- O'Toole, George Honorable Treachery: A History of U.S. Intelligence, Espionage, Covert Action from the American Revolution to the CIA 1991
- Lerner, Brenda Wilmoth & K. Lee Lerner, eds. Terrorism: essential primary sources Thomas Gale 2006 ISBN 978-1-4144-0621-3
- Lerner, K. Lee and Brenda Wilmoth Lerner, eds. Encyclopedia of Espionage, Intelligence and Security 2003 1100 pages.
- Knightley, Philip The Second Oldest Profession: Spies and Spying in the Twentieth Century Norton 1986
- Kahn, David The Codebreakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet 1996 Revised edition. First published in 1967.
- Johnson, Robert Spying for Empire: The Great Game in Central and South Asia, 1757-1947 London: Greenhill 2006
- Friedman, George America's Secret War: Inside the Hidden Worldwide Struggle Between the United States and Its Enemies 2005
- Doyle, David W., A Memoir of True Men and Traitors (2000)
- Tunney, Thomas Joseph and Paul Merrick Hollister Throttled!: The Detection of the German and Anarchist Bomb Plotters Boston: Small, Maynard & company 1919 | available on Wikisource: s:Throttled!
- Beesly, Patrick || Room 40 1982
- Burnham, Frederick Russell Taking Chances 1944
- May, Ernest (ed.) Knowing One's Enemies: Intelligence Assessment before the Two World Wars 1984
- Tuchman, Barbara W. The Zimmermann Telegram Ballantine Books 1966
[edit] World War II: 1939–1945
| Author(s) | Title | Publisher | Date | Notes |
| Babington-Smith, Constance | Air Spy: The Story of Photo Intelligence in World War II | - | 1957 | - |
| Bryden, John | Best-Kept Secret: Canadian Secret Intelligence in the Second World War | Lester | 1993 | - |
| Hinsley, F. H. and Alan Stripp | Codebreakers: The Inside Story of Bletchley Park | - | 2001 | - |
| Hinsley, F. H. | British Intelligence in the Second World War | - | 1996 | Abridged version of multivolume official history. |
| Hohne, Heinz | Canaris: Hitler's Master Spy | - | 1979 | - |
| Jones, R. V. | The Wizard War: British Scientific Intelligence 1939-1945 | - | 1978 | - |
| Kahn, David | Hitler's Spies: German Military Intelligence in World War II' | - | 1978 | - |
| Kahn, David | Seizing the Enigma: The Race to Break the German U-Boat Codes, 1939-1943 | - | 1991 | FACE |
| Kitson, Simon | The Hunt for Nazi Spies: Fighting Espionage in Vichy France | - | 2008 | |
| Lewin, Ronald | The American Magic: Codes, Ciphers and the Defeat of Japan | - | 1982 | - |
| Masterman, J. C. | The Double Cross System in the War of 1935 to 1945 | Yale | 1972 | - |
| Persico, Joseph | Roosevelt's Secret War: FDR and World War II Espionage | - | 2001 | - |
| Persico, Joseph | Casey: The Lives and Secrets of William J. Casey-From the OSS to the CIA | - | 1991 | - |
| Ronnie, Art | Counterfeit Hero: Fritz Duquesne, Adventurer and Spy | - | 1995 | ISBN 1-55750-733-3 |
| Sayers, Michael & Albert E. Kahn | Sabotage! The Secret War Against America | - | 1942 | - |
| Smith, Richard Harris | OSS: The Secret History of America's First Central Intelligence Agency | - | 2005 | - |
| Stanley, Roy M. | World War II Photo Intelligence | - | 1981 | - |
| Wark, Wesley | The Ultimate Enemy: British Intelligence and Nazi Germany, 1933-1939 | - | 1985 | - |
| Wark, Wesley | "Cryptographic Innocence: The Origins of Signals Intelligence in Canada in the Second World War" in Journal of Contemporary History 22 | - | 1987 | - |
| West, Nigel | Secret War: The Story of SOE, Britain's Wartime Sabotage Organization | - | 1992 | - |
| Winterbotham, F. W. | The Ultra Secret | Harper & Row | 1974 | - |
| Winterbotham, F. W. | The Nazi Connection | Harper & Row | 1978 | - |
| Cowburn, B. | No Cloak No Dagger | Brown, Watson, Ltd. | 1960 | - |
| Wohlstetter, Roberta. | Pearl Harbor: Warning and Decision | - | 1962 | - |
[edit] Cold War era: 1945–1991
| Author(s) | Title | Publisher | Date | Notes | |
| Aldrich, Richard J. | The Hidden Hand: Britain, America and Cold War Secret Intelligence | - | 2002 | - | |
| Ambrose, Stephen E. | Ike's Spies: Eisenhower and the Intelligence Establishment | - | 1981- | - | |
| Andrew, Christopher and Vasili Mitrokhin | The Sword and the Shield: The Mitrokhin Archive and the Secret History of the KGB | Basic Books | 1991, 2005 | ISBN 0465003117 | |
| Andrew, Christopher, and Oleg Gordievsky | KGB: The Inside Story of Its Foreign Operations from Lenin to Gorbachev | - | 1990 | - | |
| Aronoff, Myron J. | The Spy Novels of John Le Carré: Balancing Ethics and Politics | - | 1999 | - | |
| Bissell, Richard | Reflections of a Cold Warrior: From Yalta to the Bay of Pigs' | - | 1996 | - | |
| Bogle, Lori, ed. | Cold War Espionage and Spying | - | 2001- | essays | |
| Christopher Andrew and Vasili Mitrokhin | The World Was Going Our Way: The KGB and the Battle for the Third World | - | - | - | |
| Christopher Andrew and Vasili Mitrokhin | The Mitrokhin Archive: The KGB in Europe and the West | Gardners Books | 2000 | ISBN 978-0-14-028487-4 | |
| Colella, Jim | My Life as an Italian Mafioso Spy | - | 2000 | - | |
| Craig, R. Bruce | Treasonable Doubt: The Harry Dexter Spy Case | University Press of Kansas | 2004 | ISBN 978-0-7006-1311-3 | |
| Dorril, Stephen | MI6: Inside the Covert World of Her Majesty's Secret Intelligence Service | - | 2000 | - | |
| Dziak, John J. | Chekisty: A History of the KGB | - | 1988 | - | |
| Gates, Robert M. | From The Shadows: The Ultimate Insider's Story Of Five Presidents And How They Won The Cold War' | - | 1997 | - | |
| Frost, Mike and Michel Gratton | Spyworld: Inside the Canadian and American Intelligence Establishments | Doubleday Canada | 1994 | - | |
| Haynes, John Earl, and Harvey Klehr | Venona: Decoding Soviet Espionage in America | - | 1999 | - | |
| Helms, Richard | A Look over My Shoulder: A Life in the Central Intelligence Agency | - | 2003 | - | |
| Koehler, John O. | Stasi: The Untold Story of the East German Secret Police' | - | 1999 | - | |
| Persico, Joseph | Casey: The Lives and Secrets of William J. Casey-From the OSS to the CIA | - | 1991 | - | |
| Murphy, David E., Sergei A. Kondrashev, and George Bailey | Battleground Berlin: CIA vs. KGB in the Cold War | - | 1997 | - | |
| Prados, John | Presidents' Secret Wars: CIA and Pentagon Covert Operations Since World War II | - | 1996 | - | |
| Rositzke, Harry. | The CIA's Secret Operations: Espionage, Counterespionage, and Covert Action | - | 1988 | - | |
| Srodes, James | Allen Dulles: Master of Spies | Regnery | 2000 | CIA head to 1961 | |
| Sontag Sherry, and Christopher Drew | Blind Man's Bluff: The Untold Story of American Submarine Espinonage | Harper | 1998 | ||
| Encyclopedia of Cold War Espionage, Spies and Secret Operations | Greenwood Press/Questia | 2004 | - |
- Anderson, Nicholas NOC Enigma Books 2009 - Post Cold War era
- Ishmael Jones The Human Factor: Inside the CIA's Dysfunctional Intelligence Culture Encounter Books 2008, rev. 2010
- Michael Ross The Volunteer: The Incredible True Story of an Israeli Spy on the Trail of International Terrorists McClelland & Stewart 2007, rev. 2008
[edit] External links
| Look up espionage in Wiktionary, the free dictionary. |
| Wikiquote has a collection of quotations related to: Espionage |
- An Interactive Rosenberg Espionage Ring Timeline and Archive
- GCHQ: Britain's Most Secret Intelligence Agency
|
|
|
|
|
|
|
|





 选择“Disable on www.wenxuecity.com”
选择“Disable on www.wenxuecity.com”
 选择“don't run on pages on this domain”
选择“don't run on pages on this domain”